GoPlus Emergency Alert: Adobe Allegedly Hacked, Data Breach Exposes 13 Million Users

GoPlus issued an emergency alert on April 3: Adobe is suspected to have been the target of a targeted attack, putting approximately 13,000,000 users’ data at risk of exposure. The incident was disclosed by International Cyber Digest, where a threat actor identified as “Mr. Raccoon” claimed to have infiltrated Adobe systems.
Supply-Chain Attack Path: From an Indian Outsourcer to Adobe’s Core Systems
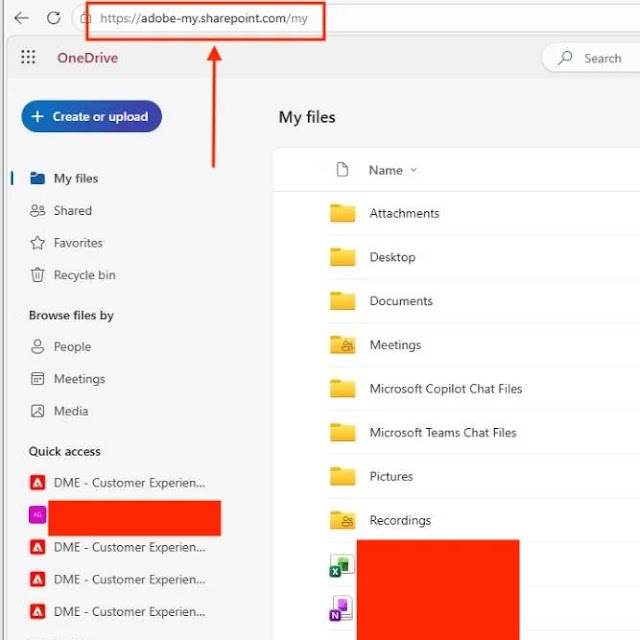
The entry point of this attack was not Adobe’s direct infrastructure, but rather a business process outsourcing (BPO) company in India that Adobe contracted. This is a typical supply-chain attack scenario. The attackers deployed a remote access trojan (RAT) on a computer of an employee at the BPO company via malicious emails to gain an initial foothold. After that, they used spear-phishing to target the employee’s supervisor, further expanding the scope of network control.
The deployed RAT can not only access documents on the target computer, but also activate the device’s network camera and intercept private communications transmitted via WhatsApp—providing deep access capabilities that far exceed typical office device intrusions. This path reveals systematic gaps in third-party vendors’ security controls when enterprises outsource core business processes.
The High Risk of Exposed Data: Full Disclosure of Support Ticket Data to HackerOne Zero-Day Submissions
The dataset suspected to have been leaked is especially sensitive in nature and includes multiple high-value types of information:
13,000,000 support tickets: includes customer names, email addresses, account details, and descriptions of technical issues—ideal material for precise phishing and identity theft
15,000 employee records: information about internal personnel at the company, which could be used for deeper social engineering attacks
All HackerOne bounty submission records: the most destructive portion—includes unpublished security vulnerabilities reported by security researchers; before patches are released, once these zero-day vulnerability details fall into the hands of malicious attackers, they will provide ready-made paths for follow-on attacks
Various internal documents: specific scope to be confirmed further
GoPlus User Safety Recommendations: Protective Measures to Take Immediately
In response to this incident, GoPlus advises users affected by Adobe services to take the following steps immediately: first, enable multi-factor authentication (2FA) to ensure that even if a password is leaked, it won’t directly lead to account takeover; second, change passwords for Adobe-related accounts to make sure they are not reused across multiple platforms; third, remain highly vigilant toward any calls or emails that claim to be “Adobe official customer support,” as leaked support ticket information could be used for highly targeted social-engineering scams.
GoPlus also reminds users to remember the “four don’ts” anti-phishing rule: don’t click on unknown links, don’t install software of unknown origin, don’t sign for unknown transactions, and don’t transfer money to unverified addresses.
Frequently Asked Questions
Has Adobe officially confirmed this data breach?
As of now, Adobe has not released any official statement confirming or denying this incident. The available information mainly comes from the threat actor’s own statements and the report from International Cyber Digest; Adobe’s official response or independent third-party verification is still pending. Users should take preventive measures before the information is clearly established.
Why is the leakage of HackerOne bounty submission records particularly dangerous?
HackerOne submission records include unpublished security vulnerabilities reported by security researchers in the bounty program. These are “zero-day vulnerabilities” in nature before Adobe completes remediation and releases patches. If they fall into the hands of malicious attackers, they could be used immediately for new attacks targeting Adobe products—putting individual and enterprise users who rely on Adobe software at direct risk.
How do supply-chain attacks bypass a company’s own security measures?
Supply-chain attacks infiltrate a target company’s outsourced vendors, bypassing the company’s own security boundaries. Even if Adobe’s own security measures are strict, if the contracted third-party BPO company’s security standards are not up to par, it can still become the attackers’ entry point. Security experts recommend conducting regular audits of all third-party vendors that have data access permissions and strictly limiting who can use bulk data export functionality.