Bitcoin quantum threat accelerates, Satoshi Nakamoto’s 2010 transition plan draws renewed attention
April 1, Bitcoin’s creator Satoshi Nakamoto attracted attention with a 2010 post. In the Bitcointalk forum, he responded to the risk of quantum computers breaking Bitcoin and proposed that a smooth transition could be achieved by implementing a progressively upgraded digital signature algorithm, indicating that the Bitcoin network has a path to respond in an orderly way to quantum threats. Recently, Google’s latest research shows that quantum computers may break Bitcoin encryption earlier than expected.
Satoshi Nakamoto’s 2010 Quantum Response: Reserve Upgrade Space Instead of Denying the Threat
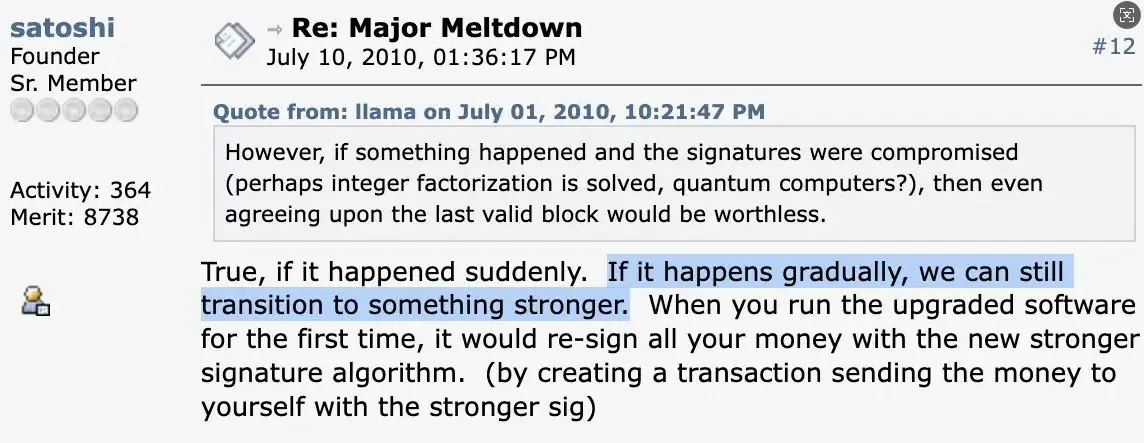 (Source: Bitcointalk forum)
(Source: Bitcointalk forum)
In 2010, a Bitcointalk forum user asked Satoshi Nakamoto: if quantum computers are strong enough, can they break the Elliptic Curve Digital Signature Algorithm (ECDSA) that Bitcoin relies on? Satoshi Nakamoto’s response demonstrated his long-term design thinking about technical evolution.
He said that if the quantum threat does become reality, the Bitcoin network can transition in an orderly manner to a stronger public-key algorithm through a gradual upgrade process. The entire process can be carried out smoothly without causing system collapse or asset losses. The core logic behind this view is that ECDSA is only a replaceable layer in Bitcoin’s security architecture, not an unchangeable design foundation. From the very beginning, Satoshi Nakamoto left room for technological evolution in the protocol design.
Real-World Progress on Quantum Threats: Google and the Ethereum Foundation’s Latest Actions
This forum statement by Satoshi Nakamoto regained attention in 2026 because the real-world quantum threat is accelerating. Google’s recent research found that quantum computers may have the computational capability to threaten Bitcoin’s elliptic curve cryptography earlier than the industry had generally predicted. The Ethereum Foundation has also established a post-quantum security dedicated team after its formation, planning to complete the post-quantum upgrade at the protocol layer by 2029, showing that major public chains are actively assessing quantum risks and rolling out long-term countermeasures.
At present, Bitcoin’s security structure relies on ECDSA to protect users’ private keys, and the SHA-256 hashing algorithm to protect the structure of the blockchain. If quantum computers reach a sufficiently large quantum-bit scale, they may, in theory, break ECDSA protection through Shor’s algorithm, enabling attackers with quantum computing power to forge transaction signatures.
Bitcoin’s Post-Quantum Upgrade Path: The Technical Direction Is Clear
Post-Quantum Cryptography research worldwide has entered a phase of accelerated development. The U.S. National Institute of Standards and Technology (NIST) has completed certifications for multiple post-quantum cryptography standards. Currently, the widely discussed upgrade paths for Bitcoin include:
Replace signature algorithms: Use post-quantum signature schemes such as CRYSTALS-Dilithium, which have been certified by NIST, to gradually replace the current ECDSA, corresponding to Satoshi Nakamoto’s described “upgrade to a stronger public-key algorithm”
Gradual address migration: Set a transition window for existing Bitcoin addresses, allowing holders to move assets to post-quantum-secure addresses before the quantum threat actually arrives, reducing system disruption
BIP governance process: Any algorithm upgrade at the protocol layer must go through the Bitcoin Improvement Proposal (BIP) process and obtain broad network-wide consensus from miners and node operators
This transition framework closely matches the “smooth upgrade” path described by Satoshi Nakamoto in 2010, and also confirms the foresight of his protocol design.
Frequently Asked Questions
What was Satoshi Nakamoto’s specific stance on quantum threats in 2010?
Satoshi Nakamoto said in the Bitcointalk forum that if quantum computers truly posed a substantive threat to Bitcoin’s ECDSA signature algorithm, the Bitcoin network could transition in an orderly manner to a post-quantum-secure algorithm through a progressively upgraded digital signature algorithm, without any systematic collapse or assets being reduced to zero.
Can quantum computers currently break Bitcoin?
At present, the quantum-bit scale of existing quantum computers is not sufficient to pose a practical threat to Bitcoin’s ECDSA. Google’s latest research indicates that threats may arrive earlier than expected, but the industry generally estimates there is still a response window of several years to more than a decade, providing time for the Bitcoin community to deploy post-quantum upgrades.
How is the Bitcoin community currently preparing to address quantum threats?
Post-quantum cryptography upgrades have been included on the research schedules of Bitcoin and multiple major public chains. NIST has completed certifications for post-quantum cryptography standards. The Ethereum Foundation has also formed a post-quantum security team and set a specific upgrade timeline. Any protocol upgrade for Bitcoin must go through the BIP process and achieve network-wide consensus. The transition timeline is relatively long, but the technical path is becoming increasingly clear.